Encryption at relaxation is a cloud baseline, however for enterprises working in extremely regulated environments, organizations should management the basis of belief. Lakebase Buyer Managed Keys (CMK) delivers this management by permitting you to make use of your individual encryption keys out of your Key Administration Service (KMS) e.g. AWS KMS, Azure Key Vault, or Google Cloud KMS – to guard and handle information throughout the complete Lakebase lifecycle.
Lakebase Buyer-Managed Keys (CMK) gives complete administration and management throughout the complete structure, in contrast to standard managed databases. Whereas conventional databases sometimes solely encrypt storage, Lakebase CMK manages each persistent storage and ephemeral compute.
The Structure of Lakebase Encryption
Lakebase structure separates storage and compute into unbiased layers – a design that allows elastic scaling and serverless operations. The storage layer (Pageserver and Safekeeper) maintains long-lived, persistent information in object storage and native caches, whereas the compute layer runs unbiased Postgres cases that scale up, down, or to zero primarily based on demand.
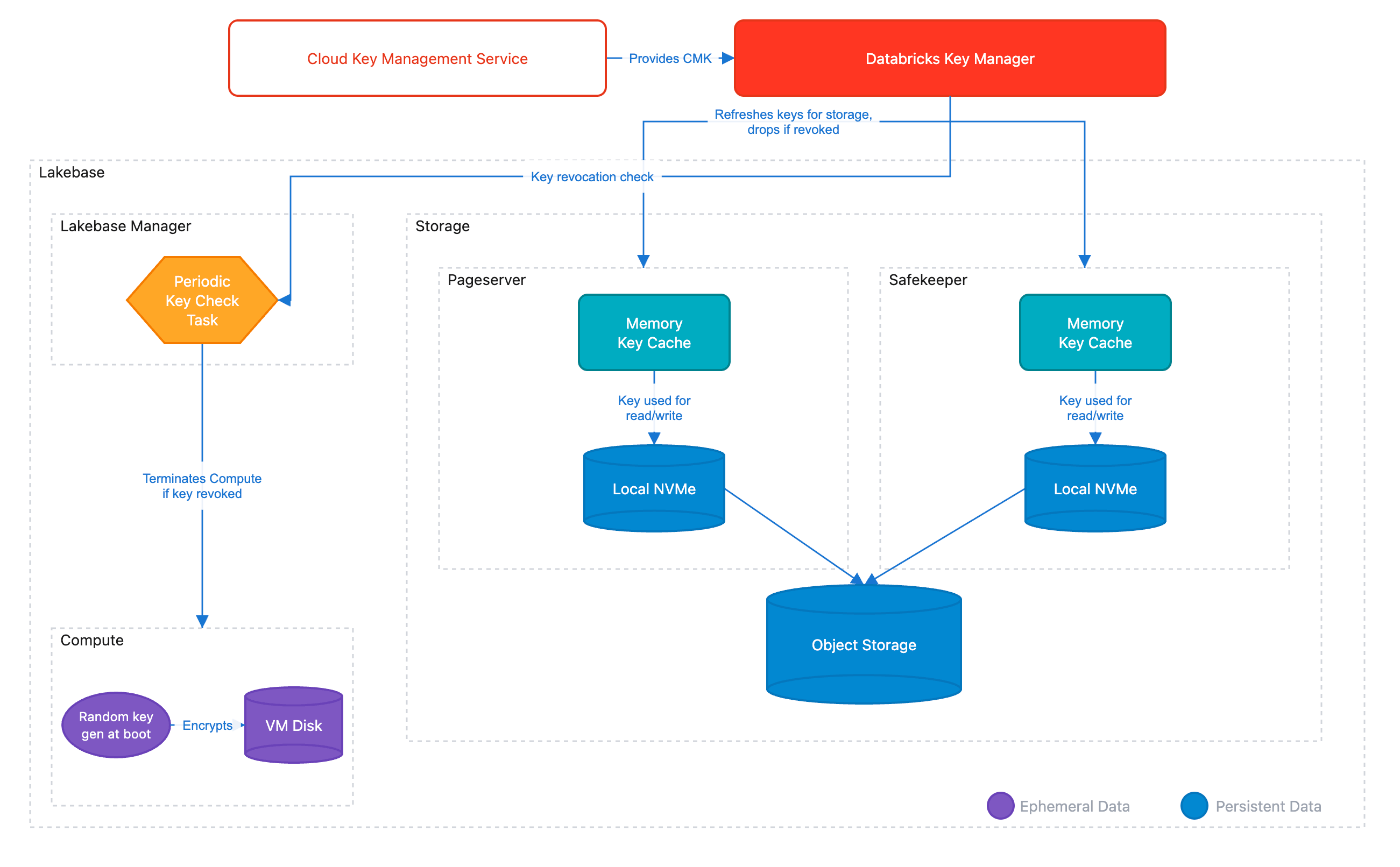
This separation creates a novel problem for encryption: each layers (in addition to all of their caches throughout the structure) should be encrypted and stay beneath buyer management. Lakebase CMK addresses this by a hierarchical Envelope Encryption mannequin.
The Key Hierarchy
Envelope Encryption is a safety mannequin the place information is encrypted with distinctive information keys (DEKs), and people keys are themselves encrypted by higher-level keys. This hierarchy ensures that your CMK by no means leaves your cloud KMS – Databricks solely receives wrapped (encrypted) variations of the keys wanted to decrypt information. The mannequin additionally allows high-performance encryption at scale, because the KMS is just contacted to unwrap keys, to not encrypt each information block. This structure is what allows seamless key rotation and well timed revocation if ever wanted.
The hierarchy consists of three ranges:
- Buyer Managed Key (CMK): The Root of Belief residing in your cloud KMS (AWS KMS, Azure Key Vault, or Google Cloud KMS). Databricks by no means sees the plaintext of this key.
- Key Encryption Key (KEK): A transient key utilized by the Databricks Key Supervisor Service to wrap information keys.
- Information Encryption Keys (DEKs): Distinctive keys generated for each information phase. These are saved alongside the information in an encrypted (wrapped) state.
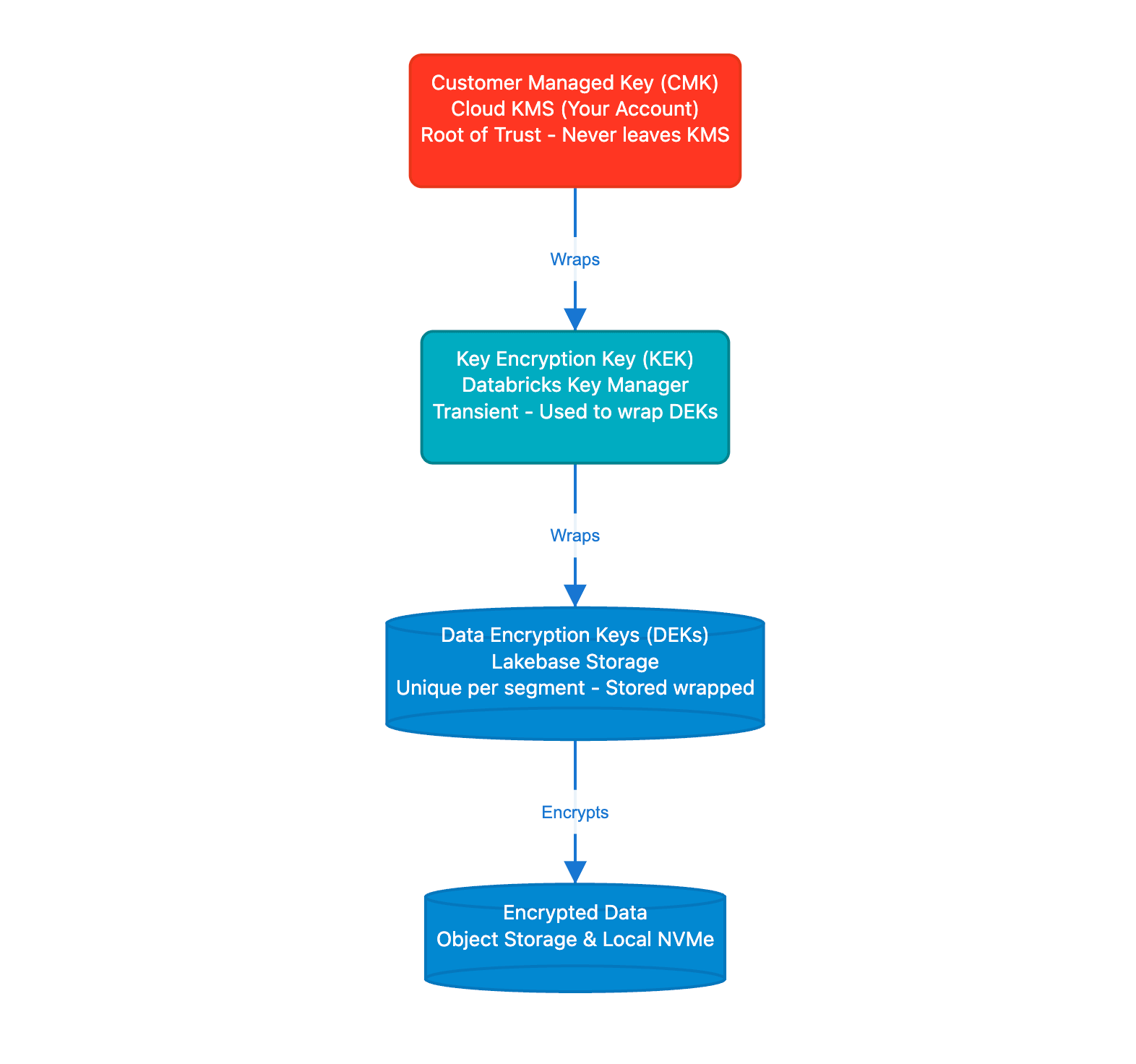
When information must be accessed, Lakebase parts unwrap the mandatory DEK utilizing keys obtained out of your KMS. Within the occasion of a revocation, the unwrapping will then fail, rendering the information cryptographically inaccessible. As a part of this course of, all ephemeral compute cases are terminated to take away entry to cached information.
CMK in Observe: Storage and Compute
The sensible implementation differs between storage and compute:
1. Persistence Layer (Storage)
All information segments managed by Lakebase, together with WAL segments (transaction logs saved by Safekeeper) and information recordsdata, are encrypted with keys protected by your CMK. This offers defense-in-depth: information at relaxation is protected by encryption keys beneath your management, not Databricks.
2. Ephemeral Layer (Compute)
The Postgres compute VM holds ephemeral information utilized by the working system and PostgresSQL – for instance, efficiency caches, WAL artifacts, temp recordsdata and so forth, So it is vital that each one of this information can also be managed beneath a CMK. CMK protects this ephemeral compute information with:
- Per Boot Keys: Each time a Lakebase compute occasion begins, it generates a novel ephemeral key.
- Automated Shredding: On CMK revocation, Lakebase Supervisor terminates the occasion, destroying ephemeral in-memory keys and rendering native disk information inaccessible.
Implementing CMK within the Lakebase Workflow
Implementation follows the usual Databricks Account to Workspace delegation mannequin. This separation of duties ensures that Safety Admins can handle keys while not having entry to the information itself. As soon as a secret’s configured on the workspace stage, all Lakebase initiatives use the CMK as a part of the encryption workflow.
Step 1: Key Configuration
An Account Admin creates a Key Configuration within the Databricks Account Console. This object accommodates the important thing identifier (ARN for AWS KMS, Key Vault URL for Azure, or Key ID for Google Cloud KMS) and the IAM position or service principal that Lakebase will assume to carry out Wrap and Unwrap operations.
Step 2: Workspace Binding
The configuration is then mapped to a selected Workspace. For Lakebase, this implies:
- New Tasks: All new Lakebase initiatives routinely inherit the workspace’s CMK.
- Isolation: Completely different workspaces can use totally different CMKs to fulfill multi tenant or multi departmental safety necessities.
Step 3: Lifecycle Administration and Rotation
Lakebase helps Seamless Key Rotation. Whenever you rotate your CMK in your cloud supplier’s console:
- The envelope encryption hierarchy allows seamless rotation – your CMK will be rotated in your cloud KMS with out re-encrypting information or altering DEKs.
- There may be zero downtime or guide re-encryption required.
Safety Auditability
As a result of the CMK resides in your cloud account, cryptographic operations towards your key are logged in your supplier’s audit service (AWS CloudTrail, Azure Monitor, or Google Cloud Audit Logs).
Get Began with Enhanced Information Sovereignty
In case your group requires the very best stage of cryptographic management over your Postgres workloads, Lakebase CMK is now accessible for Enterprise tier prospects.
Able to safe your information? Contact your Databricks account group to allow Buyer Managed Keys on your workspace, or go to our technical documentation to evaluation the prerequisite IAM insurance policies and KMS configurations.
Not but a Databricks buyer? Get began with a trial.

