Fashionable knowledge architectures more and more depend on multi-warehouse deployments to realize workload isolation, value optimization, and efficiency scaling. Amazon Redshift federated permissions simplify permissions administration throughout a number of Redshift warehouses.
With federated permissions, you register Redshift warehouse namespaces with the AWS Glue Information Catalog, making a unified catalog that spans your total warehouse fleet within the account. Registered namespaces are routinely mounted in each warehouse, offering knowledge discovery with out handbook configuration. You may outline permissions on database objects utilizing acquainted Redshift SQL instructions, specifying international identities by AWS Identification and Entry Administration (IAM) or AWS IAM Identification Heart (IDC). These permissions are saved alongside the warehouse knowledge and enforced constantly, no matter which warehouse runs the question. This supplies a unified and safe entry management mannequin throughout your Redshift surroundings.
On this submit, we present you the right way to outline knowledge permissions one time and routinely implement them throughout warehouses in your AWS account, eradicating the necessity to re-create safety insurance policies in every warehouse.
Key capabilities of Amazon Redshift federated permissions
Federated permissions in Amazon Redshift supply the next key capabilities:
- International identification integration – Federated permissions use IAM and IAM Identification Heart to supply single sign-on (SSO) throughout all registered warehouses. Customers authenticate one time by their current identification supplier (IdP) and obtain constant entry based mostly on their international identification, no matter which warehouse they connect with. This alleviates the necessity to create and handle separate person accounts in every warehouse, lowering administrative overhead and bettering the person expertise.
- Unified catalog with computerized mounting – If you register a Redshift namespace with the Information Catalog utilizing federated permissions, it turns into routinely seen in all warehouses inside your account. Analysts utilizing the Amazon Redshift Question Editor v2 or their most popular SQL consumer can uncover and question tables throughout registered warehouses with out handbook catalog configuration. This computerized mounting functionality simplifies knowledge discovery and allows cross-warehouse analytics.
- Constant fine-grained entry management – Row-level safety (RLS) insurance policies, dynamic knowledge masking (DDM) insurance policies, and column-level safety (CLS) outlined on warehouses utilizing Amazon Redshift federated permissions routinely implement when knowledge is queried from consuming warehouses. You may implement superior entry controls—akin to AWS Area-based row filtering, role-based masking for delicate columns like SSN or bank card numbers, and time-based entry restrictions—with confidence that these insurance policies apply throughout warehouses.
- SQL-based permission administration – Federated permissions use acquainted Redshift SQL syntax for permission administration. You create RLS insurance policies with
CREATE RLS POLICY, connect them to tables and roles withATTACH RLS POLICY, outline masking insurance policies withCREATE MASKING POLICY, and grant permissions with commonplaceGRANTstatements. This SQL interface allows infrastructure as code (IaC) approaches, helps database directors to make use of their current abilities, and integrates naturally with current extract, remodel, and cargo (ETL) and automation workflows that use IAM or IAM Identification Heart authentication.
Multi-warehouse structure with federated permissions
The multi-warehouse structure with federated permissions in Amazon Redshift represents an information mesh method the place a number of unbiased compute sources function on shared knowledge with unified governance. The next diagram illustrates the Redshift federated permissions setup course of with the Information Catalog.

The method consists of the next steps:
- Every Redshift warehouse (1,2…N) registers with the Information Catalog. Refer onboarding documentation on registering the warehouse.
- After you register your Redshift warehouses with the Information Catalog, you may question knowledge throughout your warehouses. Registered catalogs are routinely mounted in each warehouse within the account, showing within the database explorer of Question Editor v2, and SQL shoppers linked to Amazon Redshift. To question a desk in a registered catalog, use the three-part naming conference:
database@catalog_name.schema_name.table_name. - If you run a cross-catalog question, Amazon Redshift propagates your international identification (IAM position or IAM Identification Heart person) to the distant warehouse. The distant warehouse’s catalog occasion validates your permissions in opposition to the grants and fine-grained entry management insurance policies outlined on the queried tables. When you’ve got the mandatory permissions, the desk metadata and any relevant RLS, DDM, or CLS insurance policies are returned to the consuming warehouse. Your native warehouse’s compute occasion integrates these safety insurance policies into the question execution plan and runs the question on Redshift Managed Storage (RMS).
The enforcement of fine-grained entry controls on distant knowledge is a key differentiator of federated permissions. Conventional Redshift knowledge sharing doesn’t assist RLS or DDM insurance policies on shared tables. With federated permissions, the safety insurance policies outlined on the distant warehouse routinely apply when knowledge is queried from any shopper warehouse. This helps compliance with knowledge governance necessities with out requiring directors to duplicate safety insurance policies throughout warehouses.
The multi-warehouse structure scales horizontally with out growing governance complexity. If you add a brand new warehouse to your account and register it with federated permissions, it routinely inherits the suitable permission mannequin with out handbook configuration. Analysts connecting to the brand new warehouse instantly see all databases they’ve entry to throughout the mesh, and all safety insurance policies apply routinely. This alleviates the N-squared downside of managing permissions throughout N warehouses, lowering the executive burden from N separate configurations to a single unified governance mannequin.
Question lifecycle
The next diagram illustrates the step-by-step movement of how a person question on Redshift Warehouse 1 accesses objects in Redshift Warehouse N with federated permissions.

Observe: Steps 2, 3, and 4 shall be skipped if permission particulars can be found within the native cache
The workflow consists of the next steps:
- The person connects to Redshift Warehouse 1 and queries a desk in Federated Catalog N.
- Redshift Warehouse 1 calls the Information Catalog
GetTableAPI. This request contains the person’s token. - The request routes to Redshift Warehouse N.
- Redshift Warehouse N verifies the person permissions. If it’s approved, it returns the desk metadata and safety coverage particulars akin to RLS insurance policies, DDM guidelines, and CLS settings.
- Redshift Warehouse 1 applies the safety insurance policies within the question plan and runs the question in opposition to Redshift Managed Storage (RMS), the place Redshift shops knowledge in an optimized format.
- The outcomes are returned to the person.
Answer overview
The instance on this submit demonstrates the right way to outline RLS and DDM insurance policies on an information warehouse and confirm that these insurance policies are enforced when querying from one other knowledge warehouse.
We are going to create a desk with bank card knowledge and apply RLS and DDM insurance policies to restrict shopper playing cards knowledge and masks bank card values for non-admin customers. These insurance policies shall be utilized throughout all the information warehouses constantly and masks the bank card particulars when non-admin customers question the desk.
Stipulations
Create the next IAM roles:
Create desk and cargo knowledge
Run following steps to create a credit_card desk and cargo pattern knowledge.
- Hook up with the primary Redshift knowledge warehouse1 utilizing the IAM Aadmin position
- Create a credit_cards desk
- Insert pattern knowledge
Apply RLS and DDM insurance policies
Run following steps to create and apply RLS and DDM insurance policies.
- Create an RLS coverage to filter solely shopper card varieties:
- Create a DDM coverage that masks bank cards:
- Connect RLS and DDM Insurance policies to RedOnly position
- Allow Row Stage Safety on the desk
- Grant choose on the desk to Readonly position
Hook up with knowledge warehouse 2 as read-only person
Run following steps on knowledge warehouse 2 to question the information.
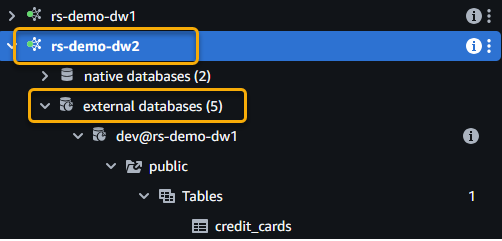
- Hook up with knowledge warehouse 2 as a read-only person and increase the exterior databases. The next screenshot exhibits an instance utilizing Question Editor V2.
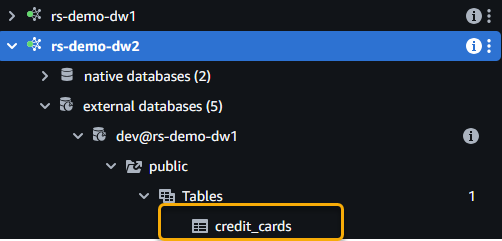
- Discover the
credit_cardsdesk from knowledge warehouse 1 once you increase the catalog.
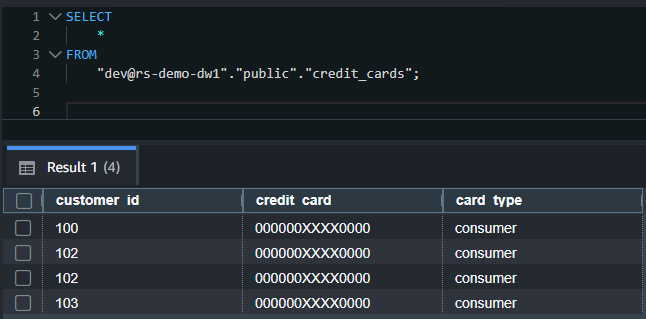
- Run the next SQL to question the desk. Exchange
rs-demo-dw1within the following SQL with the catalog title you gave whereas registering knowledge warehouse 1: - It is best to see solely
shoppersort bank cards with card particulars masked within the output. The RLS and DDM insurance policies utilized in knowledge warehouse 1 on theIAMR:ReadOnlyperson are enforced regardless that you queried the desk from a distinct knowledge warehouse.
The next screenshot exhibits an instance output.
- For auditing, you may run
SHOWinstructions to view the insurance policies utilized on the tables for the roles:
This instance demonstrates the facility of federated permissions: safety insurance policies outlined one time on a warehouse routinely implement throughout your warehouses, sustaining compliance with out duplicating coverage definitions.
Issues
Be mindful the next when utilizing federated permissions:
Clear up
To keep away from incurring future expenses, delete the sources you created, together with the Redshift knowledge warehouses and IAM roles.
Conclusion
Amazon Redshift federated permissions remodel multi-warehouse knowledge governance right into a streamlined, automated course of. For organizations working a number of Redshift warehouses, federated permissions ship quick worth by lowering administrative time and supporting constant safety enforcement. The acquainted SQL interface and backward compatibility with current Redshift permissions allow fast adoption with out requiring groups to study new governance fashions.
The combination with IAM and IAM Identification Heart supplies enterprise-grade identification administration with SSO capabilities, and the automated mounting of registered catalogs simplifies knowledge discovery and cross-warehouse analytics. If you’re presently utilizing Amazon Redshift native permissions, discuss with the software described in Modernize Amazon Redshift authentication by migrating person administration to AWS IAM Identification Heart.
To study extra and get began, see Amazon Redshift Federated Permissions documentation.
Concerning the authors

