With over 470 million related automobiles anticipated by finish of 2025, defending delicate automobile information, notably Car Identification Numbers (VINs), has change into essential for automakers. VINs function distinctive identifiers in automotive processes from manufacturing to upkeep, making them enticing targets for cybercriminals. This put up explores how automakers may also help securing VINs in related automobile platforms utilizing AWS IoT serving to guarantee each information safety and system performance.
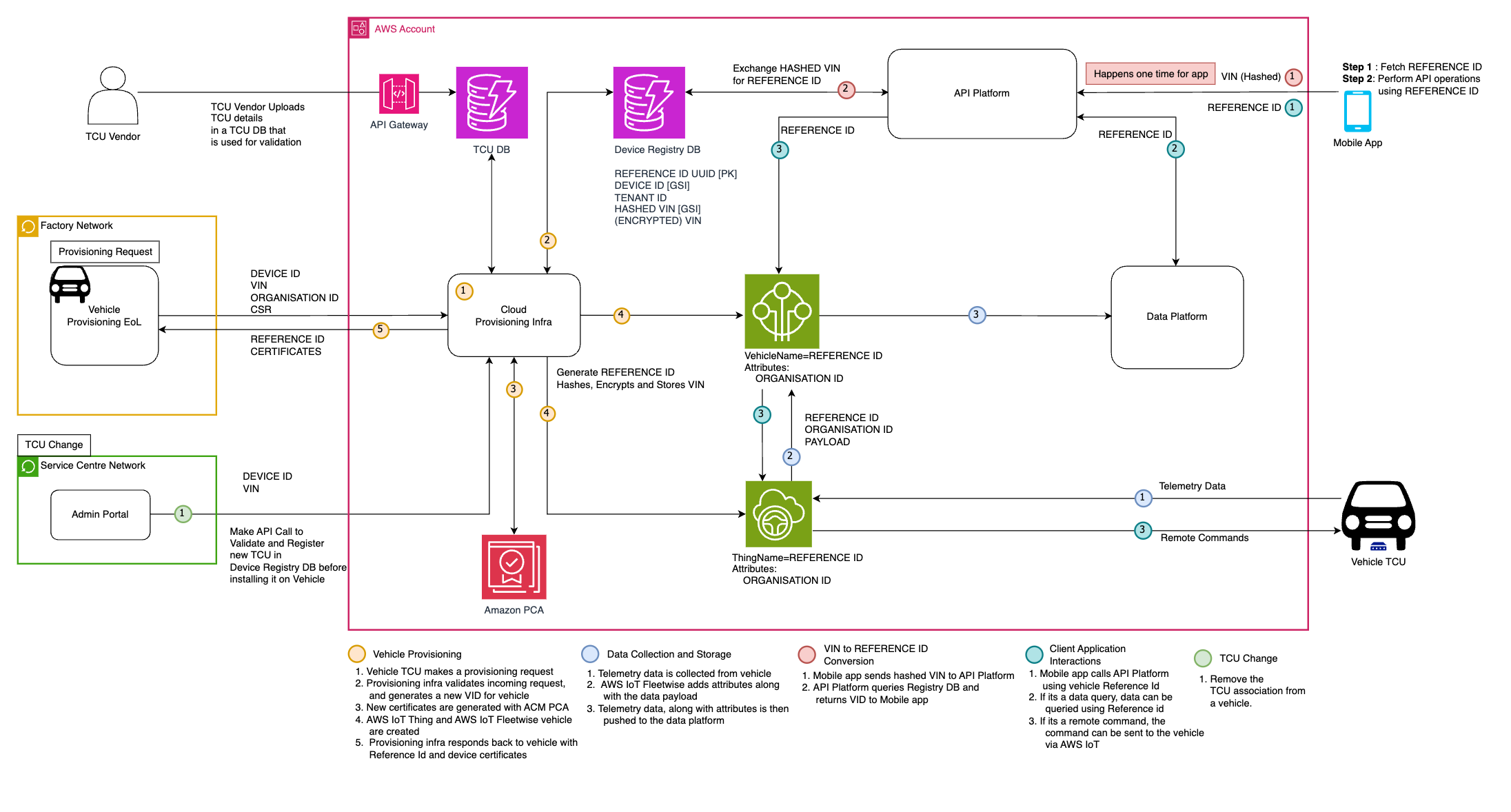
This answer introduces Reference IDs as pseudonyms for VINs, serving to allow safe automobile information interactions with out exposing precise VINs. Utilizing AWS IoT providers, we’ll exhibit how this structure helps automakers defend delicate information whereas sustaining full performance throughout automotive use instances.
Introduction
The answer makes use of a Reference ID system the place every automobile receives a novel identifier throughout provisioning, performing as a VIN proxy in all platform interactions. A automobile registry database shops each hashed and encrypted variations of VINs, mapped to their Reference IDs. When purchasers current a VIN, the system hashes it to retrieve the corresponding Reference ID, enabling safe integration with present processes.
The encrypted VIN is added as a fail-safe measure, encrypted throughout provisioning utilizing a safe AWS Key Administration Service (AWS KMS). In instances the place the plain textual content worth of the VIN must be retrieved, it may be completed by decrypting this worth, making certain that the precise VIN is accessible when completely obligatory whereas sustaining robust safety measures.
VINs include vital automobile info (producer, mannequin, yr) and could be linked to private information. Unprotected VINs in cloud environments threat id theft, automobile theft, insurance coverage fraud, privateness violations, and regulatory non-compliance (GDPR, CCPA).
By implementing a Reference ID system for VIN safety in cloud-based related automobile platforms, automakers may also help improve information safety whereas sustaining the performance and effectivity required for contemporary automotive operations:
- They act as proxies for VINs, enhancing safety and information minimization
- Help compliance with information safety laws
- Present versatile entry management and improved audit-ability
- Provide scalability for giant automobile fleets and simpler system interoperability
- Enable for revocation with out altering the underlying VIN
- Allow detailed auditing and logging of VIN entry and transformations, offering visibility into who/what has authorization to transform between Reference IDs and VINs
Structure walkthrough
1. Reference ID
A Reference ID is a UUID generated throughout automobile provisioning that serves as a VIN proxy all through the automobile’s lifecycle, creating an abstraction layer that protects delicate VIN information.
2. Car registry database
The automobile registry database serves as a centralized repository for automobile info all through its platform lifetime. Key options embody:
- Reference ID to hashed VIN mapping
- Encrypted VIN storage
- Car provisioning and state change monitoring
- Gadget change historical past
- Car attributes and configurations
VIN hashing allows safe verification with out exposing precise values. This centralized method gives a single supply of reality whereas enabling safe distant diagnostics and over-the-air updates.
| Car Registry DB |
| referenceId – Partition key |
| deviceId – International secondary index |
| hashedVin – International secondary index |
| tenantId |
| encryptedVin |
Notice: deviceId and hashedVin being International Secondary Indexes allows querying automobile particulars by both subject.
3. Car provisioning
Car provisioning establishes safe automobile administration and implements the reference ID system via information validation, safe storage, and AWS IoT integration.
Let’s stroll via the important thing steps of this course of to know the way it safeguards automobile info whereas enabling seamless connectivity and administration:
3.1 Knowledge validation:
- The provisioning infrastructure hashes the VIN and queries the automobile registry DB to verify if it’s a first-time provisioning.
- For brand new autos, DEVICE ID could be validated towards present information made obtainable by the TCU Producer.
- It additionally checks if the DEVICE is already hooked up to a different automobile by querying the automobile registry DB with DEVICE ID.
3.2 Reference ID technology:
- A question is carried out towards the automobile registry DB to validate if automobile is already provisioned utilizing hashed VIN.
- If automobile isn’t provisioned already, a brand new UUID is generated because the Reference ID.
- The Reference ID, hashed VIN and encrypted VIN (through KMS) are saved within the automobile registry DB together with different automobile info. Within the uncommon occasion of a UUID collision, the request could be re-tried to generate a brand new UUID as Reference ID.
- A last question is carried out by Reference ID within the automobile registry DB to make sure uniqueness. If UUID collision is detected, a brand new UUID is generated.
- For beforehand provisioned autos, the incoming payload is solely validated towards the registry DB entry.
3.3 Certificates technology:
- Certificates are generated utilizing ACM PCA with Widespread Title = Reference ID.
3.4 AWS IoT integration:
- An AWS IoT Factor is created with Factor identify = Reference ID.
- An AWS IoT FleetWise Car is created with Car Title = Reference ID.
3.5 Response payload:
- After profitable provisioning the automobile is supplied with Certificates and Reference ID.
- The automobile can hook up with AWS IoT FleetWise utilizing the returned certificates and ClientId = ReferenceID.
This course of helps guarantee safe provisioning of autos whereas defending delicate VIN info utilizing Reference IDs, leveraging AWS providers for strong id and entry administration. The automobile can present a Certificates Signing Request (CSR), which the provisioning infrastructure makes use of to generate the certificates.
4. Knowledge assortment and storage
Knowledge assortment and storage is an integral part the place Reference IDs guarantee safe dealing with of car information all through its lifecycle – from transmission to storage and retrieval. This method helps defend VIN info whereas enabling environment friendly information operations.
4.1 Car to AWS IoT FleetWise:
- Car connects to AWS IoT FleetWise utilizing the Reference ID because the consumer ID.
- All information despatched from the automobile is related to the Reference ID, because the automobile identify in AWS IoT FleetWise = Reference ID.
4.2 AWS IoT FleetWise to information platform:
- Knowledge flowing from AWS IoT FleetWise is enriched with the automobile identify (Reference ID).
4.3 Knowledge storage and retrieval:
- Knowledge within the information platform is saved utilizing the Reference ID because the identifier.
- Cell app queries the information platform through the API Platform utilizing the Reference ID to retrieve automobile information.
The pseudonymous Reference ID comprises no vehicle-specific info and serves as the first identifier throughout AWS IoT Core, AWS IoT FleetWise, and related information shops. This information-neutral method helps guarantee VIN safety whereas enabling seamless information operations throughout the platform.
5. Consumer software interactions:
Consumer purposes, corresponding to Buyer Relationship Administration (CRM) techniques or platforms managing user-to-VIN mappings, usually cope with plain textual content VIN numbers. To take care of the safety advantages of this technique whereas accommodating these purposes, a streamlined course of for consumer interactions is carried out with the related autos platform.
5.1 VIN to Reference ID conversion:
- The consumer software, after verifying automobile possession, makes an API name to the platform to transform between hashed VIN and Reference ID.
- The API queries the automobile registry DB to retrieve the corresponding Reference ID.
- The Reference ID is then returned to the consumer software.
Safety concerns:
- Entry to this conversion API should be strictly managed via strong authentication and authorization.
- All conversion requests must be logged for audit functions and monitored for suspicious patterns.
- Implementation ought to embody price limiting and different safety measures to guard towards DoS/DDoS assaults and unauthorized bulk conversion makes an attempt.
- Since this API allows re-identification of car information, entry must be restricted to approved purposes with official enterprise wants.
5.2 As soon as the consumer software has obtained the Reference ID comparable to the VIN, it might probably:
- Retrieve information from the information platform utilizing the Reference ID.
- Carry out operations immediately on the automobile by passing the Reference ID corresponding to distant instructions.
This method helps improve platform safety by eliminating VIN utilization in API calls and sustaining separation between VINs and Reference IDs. The system helps allow safe consumer software interactions whereas offering a sturdy framework for cloud-based automobile administration.
6. Telematics management unit change:
The TCU (Telematics Management Unit) change move is a vital course of within the related automobile platform, addressing eventualities the place a automobile’s TCU must be up to date or changed. This could happen both earlier than the automobile leaves the manufacturing facility or after a person has taken possession and a difficulty with the TCU is found, requiring substitute at a service middle.
The TCU Change move could be made obtainable as an API name with certainly one of 2 capabilities:
- Replace the DEVICE ID within the automobile registry DB to a brand new DEVICE ID.
- Merely delete the DEVICE ID within the automobile registry DB entry of the automobile i.e. mark it as NULL.
6.1 TCU replace:
- Inputs: hashed VIN (or Reference ID), present DEVICE ID, new DEVICE ID.
- The API:
- Verifies hashed VIN exists and matches present DEVICE ID in registry database
- Checks new DEVICE ID isn’t related to one other automobile.
- Updates DEVICE ID in registry database.
- Revokes and deletes the automobile’s present certificates (issued throughout provisioning and registered in AWS IoT Core) for the reason that non-public keys are saved inside the TCU {hardware} itself, requiring new certificates for the substitute TCU.
- New TCU goes via provisioning course of to connect with cloud.
6.2 TCU delete:
- Inputs: hashed VIN (or Reference ID), present DEVICE ID.
- The API:
- Verifies hashed VIN exists and matches DEVICE ID in registry database.
- Removes DEVICE ID from registry database entry.
- Revokes and deletes the automobile’s present certificates (issued throughout provisioning and registered in AWS IoT Core)
Notice: Both hashed VIN or Reference ID can be utilized to determine the automobile. Utilizing hashed VIN is appropriate resulting from SHA256’s extraordinarily low collision likelihood.
Each flows assist guarantee a safe and trackable TCU change course of, with the registry database sustaining a historical past of TCU adjustments for every automobile. This method maintains the integrity of the system whereas accommodating obligatory {hardware} updates within the automobile fleet
Safety, efficiency, and scalability concerns
The Reference ID system enhances VIN safety by minimizing VIN publicity in every day operations. The automobile registry DB shops solely hashed and encrypted VINs, whereas Reference IDs deal with all platform interactions. Safety is additional enhanced via AWS KMS encryption and strict entry management insurance policies. For optimum efficiency and scalability, the system makes use of environment friendly UUID technology and world secondary indexes from DynamoDB for fast queries.
Trying to the longer term, this VIN administration system has the potential to combine with rising applied sciences corresponding to blockchain or distributed registry know-how for tamper-proof VIN data, additional enhancing safety and traceability. The wealth of knowledge automakers can acquire via this technique additionally opens potentialities for superior analytics and machine studying purposes, doubtlessly providing insights into automobile efficiency, upkeep wants, and person habits patterns.
To help with ongoing compliance with evolving information safety laws like GDPR and CCPA, it is strongly recommended to make use of the newest hashing and encryption algorithms, implement granular entry controls, and recurrently audit your information dealing with practices.
This complete method not solely helps safeguard VIN information but additionally positions the platform for future improvements in related automobile administration.
Conclusion
This put up demonstrated how Reference IDs may also help automakers improve VIN safety in related automobile platforms on AWS. This structure helps defend delicate automobile information whereas sustaining full performance throughout automotive use instances. By leveraging AWS providers like AWS IoT Core and Amazon DynamoDB, this answer scales effectively for giant automobile fleets.
Because the variety of related autos grows, strong safety measures change into essential for automakers. This Reference ID system not solely helps automakers safeguard VINs but additionally helps them meet compliance requirements for information safety laws. It gives a versatile framework for managing automobile id all through its lifecycle, together with eventualities like TCU adjustments.
You’re inspired to discover how this method could be tailored to your related automobile options. For extra info on AWS IoT providers and related automobile greatest practices, go to the AWS IoT FleetWise documentation and associated weblog posts
In regards to the authors





